Tags
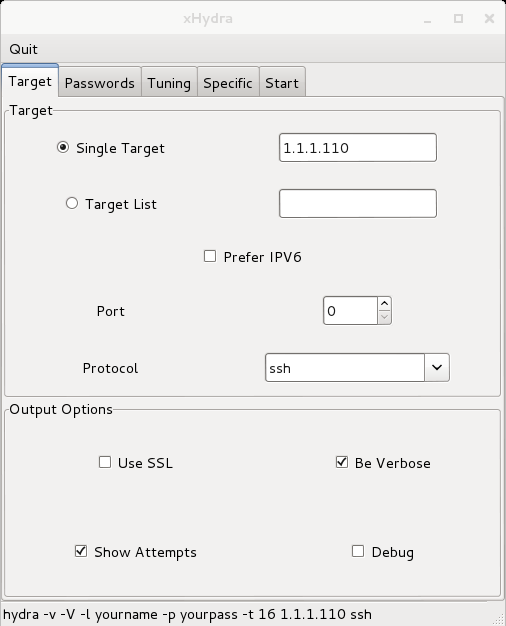
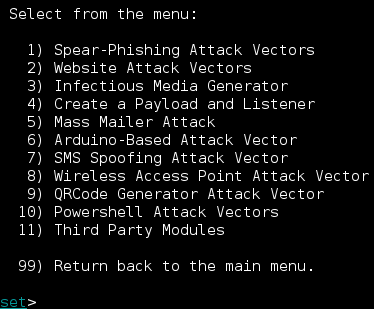
This basic tutorial will demonstrate how to crack SSH passwords with Hydra’s easy to use graphical interface (Hydra-gtk) via dictionary. Hydra-gtk comes pre loaded on Kali Linux and is listed under “Password Attacks” -> “Online Attacks”. Note that this is an online attack, meaning that this tool targets live services like SQL, ftp, irc, ssh, http, and many more and will be communicating over the network unhidden. It is not an offline hash cracking tool. Another useful feature of Hydra-gtk is that it displays the command line input at the bottom of the screen as you add options and wordlists.
Lab setup:
- Kali Linux VM with bridged networking
- Using Nmap (v6.40 at the time of this post)
- Using Hydra-gtk (v7.6 at the time of this post)
- Metasploitable 2 VM with bridged networking
Check out the resources page if you need links to the above downloads.
To begin, we will boot up Metasploitable 2 in a separate virtual machine (this will be our victim). Logging in with the default credentials (msfadmin/msfadmin), grab the ip address by using the ifconfig command:
To show that 1.1.1.110 is running an SSH server, run an Nmap -sV scan on the targeted Metasploitable address from Kali and check out the services and what ports they are running in:
..So we see that there are a ton of services being hosted here, and this is expected of a vulnerable system like Metasploitable. The service that we are interested in is SSH (on port 22).
Moving on, open Hydra-gtk and set the target to be the Metasploitable machine and the protocol as ssh. We will leave the port option empty because SSH is operating over the traditional port 22, if it were operating over an usual random port, then the attacker would want to specify that port. As for output options, my personal preference is for it to be verbose and show attempts so that actually know what is going on:
Now switch to the Passwords tab. I don’t have a username list handy, but for examples sake, I will assume that we know, and enter ‘msfadmin’. We will use a popular password list that is already on Kali called rockyou.txt (/usr/share/wordlists/). It may require you to unzip it (try: tar -xzvf rockyou.txt.gz) before you can use it here. We also want to check “Try login as password” and “Try empty password” out of good habit:
Finally, we can go to the start tab and select Start to begin our attempts. Immediately, we see that the password is found as being msfadmin. The reason it was found so quickly was not that it was in the wordlist, but because we told Hydra-gtk to try the login as the password:
One way to defend against this type of attack is to disable SSH password login and only allow SSH login with a key. An ethical way of using Hydra might be a System Administrator checking the complexity of clients’ passwords to see if they hold up against a dictionary attack. Setting a high standard for password length and complexity would deter most attackers from attempting a dictionary attack (unless their password is already in the dictionary 😕 .
Thanks for reading!